Archive for the ‘Implementation/Integration’ Category
Super Tuesday Poll – 802.1X authentication
Wi-Fi Jedi Speaking at Phoenix ISSA – 7/13
For those of you in the Phoenix area, I will be speaking at the Phoenix Information Systems Security Association chapter meeting on Tuesday, July 13th 2010. Registration starts at 11:30, and I will be speaking at noon.
I will be speaking about using Wi-Fi as a part of your Business Continuity / Disaster Recovery process. My session abstract is below as well as the invite from ISSA to attend the meeting. If you are interested in attending, there is a hyperlink at the end of the invitation.
Presentation Abstract: When disaster strikes, does your organization have the processes and technology in place to ensure continuation of business? In today’s high tech world, one important piece to restoring normal business operations is to establish a reliable computer network. The speaker will discuss the main factors in deciding in whether to deploy a wired or wireless network as a part of disaster recovery & business continuity – factors including cost, security, and reliability. The presentation also includes a case study and several recommendations to maximize value to session attendees.
Phoenix ISSA® invites you to its
Q3/10 Quarterly Training Forum to be held on:
DATE: Tuesday, July 13, 2010
TIME: 11:30 am –5 pm
PROGRAM:
1. “Wireless Security and BCP” – Douglas Haider, Xirrus
2. “End Point Security” – Parker Marshall Fishnet Security
3. “VM Security”, Diane Barrett, University of Advancing Technology
4. “Business Records to Digital Evidence”, Hoyt Kesterson, Terra Verde Services
LOCATION:
ITT Technical Institute — 5005 W. Wendler Dr., Tempe, AZ 85282
(NW Corner, I-10 & Baseline, Across from Fry’s Electronics)
Please join us! Our speakers represent security leaders in different industries who will share their insights and expertise. Stay on top of an ever-changing field, with leading edge content. Get a free lunch and snacks. Earn 4 hours CPE credits for certification maintenance (we provide the certificate). Meet and network with other security professionals. Win great door prizes!
For event details and registration go to: RSVP link
This event will be full—don’t wait to register!
Email Questions: 802.11n Deployment Using 2.4GHz and 5GHz Simultaneously
I received a following set of questions via email and thought that rather than only respond to the one individual, but post it on WiFiJedi.com for general consumption.
Here’s what I received:
I have recently done a deployment where the customer is using 802.11n in both 2.4 and 5 GHz range. I have configured a WLan with that is providing coverage for all the radios including a/b/g/n on a 4402 controller in WiSM Module. The clients are also unable to run on all the radios. Everything is working fine, but we are seeing clients that have been connected to either a 2.4ghz radio or 5ghz radio, tend to switch between them when running for a while. I am trying to understand this scenario, since there is no setting on the controller that I can find would allow the preference of the radio. we are currently running the latest 6.0 code on the WLCs. Secondly the data rates are set to 24Mbps or higher for both radios, that means 802.11b is not allowed. The client machine was sitting at one position for 24hrs that means the user was not moving around hence the roaming should not be involved I think. Lastly we did the survey for 802.11a coverage and I don’t think there is any issue with the coverage, since it connects to 802.11a at excellent. The question really is that once the client connects to 802.11a on excellent and is running on that radio for an hour perfectly and the user is not moving at all why is it that it switches itself to 802.11g and then again to 802.11a?? I wanted to get your opinion as if do you know any bugs or vulnerabilities by having both radios enable?
And here is my response:
Thank you for your message. Unfortunately, at this time most/all of the roaming decisions are made by the stations (laptops, etc.) and not the infrastructure (Access Points and WLAN Controllers). The IEEE is devising a standard to change this, but it will take some time.
What type of stations are you using? Are they laptops, or something else such as handheld scanners, Voice-over-WiFi phones, etc? If they are laptops, are they Windows or Macintosh? If you are using Windows based laptops, you may be able to set a preference for 5 GHz within the client driver. For example I have an Intel 4965 AGN adapter — if I right-click on my wireless adapter and select “properties”, then click “configure” I can select the Wireless mode to be 802.11a/n only. I can also set the roaming aggressiveness so that it roams less frequently. Macintosh computers have a natural preference for 2.4 GHz and it is more difficult to encourage them to connect to something at 5 GHz – in a case like that, you may consider adding a 5 GHz SSID on its own VLAN. Again, these roaming decisions are made by the station, so your best bet is to look at the laptop settings to see what you can tweak.
One other potential “gotcha” that came to mind was how you enabled 802.11g only. The data rates have to be carefully managed for full interoperability between the station and the infrastructure. There are two types of data rates – the “basic” rates and the “supported” rates. The basic rates should include all 802.11g rates, even below 24 Mbps (therefore you should double-check that the basic rates include 6,9,12, and 18 Mbps). The requirements for supported rates are less strict.
2.4 GHz vs. 5 GHz
This is a guest post that originally appeared on CWNP.com – the post generated a LOT of comments, so I thought I would pull it out of “the valut” and re-publish here at WiFiJedi.com
————————————————————————————-
I recently ran a poll on my blog (WiFiJedi.com) about frequency band utilization for 802.11n deployments. Here are the results:
In what frequency band do you plan to deploy 802.11n?
- 2.4 GHz = 17%
- 5 GHz = 12%
- Both (2.4 GHz and 5 GHz) = 18%
- Not sure – why does it matter? = 8%
- No plans to deploy 802.11n = 45%
Personally, I found the results surprising for two reasons. First, I was surprised by the large number of respondents who said they have no plans to deploy 802.11n. I wonder what factors are keeping them from deploying 802.11n? Price? Security? Reliability? Scalability?
Second, I was surprised by the low number of respondents who chose a pure 5 GHz 802.11n deployment. I believe there are numerous advantages to deploying WLANs in the 5 GHz band, especially when it comes to 802.11n.
Consider the following:
Number of Available Channels
There are only three non-overlapping channels in the 2.4 GHz frequency band. Channels 1, 6, and 11. There are 23 non-overlapping channels between the 5GHz lower, middle, and upper bands.
Total Capacity
Because there are many more non-overlapping channels in the 5 GHz range, it can deliver greater total capacity. 802.11g networks offer 54 Mbps of capacity on each of the three non-overlapping channels in the 2.4 GHz spectrum. This equates to a total capacity of 162 Mbps. 802.11a has the same speed, 54 Mbps, but offers a total of 1.24 Gbps of capacity across its 23 non-overlapping channels. This holds true for 802.11n networks as well. With speeds of 150 Mbps per channel, there are 450 Mbps of 802.11n capacity with 2.4 GHz use and 3.45 Gbps of capacity with 5 GHz use.
Interference
The 2.4 GHz frequency band is crowded with interfering devices. Other Wi-Fi access points, microwave ovens, cordless phones, Bluetooth devices, baby monitors, etc. all make for a noisy environment. This degrades the overall signal-to-noise ratio (SNR). The 5 GHz band is considerably cleaner in most areas – see for yourself with a spectrum analyzer!
Channel Planning
With nearly 8 times the number of channels to chose from in the 5 GHz band, planning is far simpler than in the 2.4 GHz band. I realize that most enterprise grade solutions have some sort of auto-channel or automatic radio management feature to assist with this, but co-channel interference remains a concern, especially in tight spaces or high-density environments. The additional choices in 5 GHz minimizes the possibility that two APs will utilize the same channel in the same areas.
Channel Bonding
Sure, some organizations need to support legacy devices in the 2.4 GHz spectrum. However, I don’t think it makes sense to deploy 802.11n networks in this band. One of the main technical improvements available in 802.11n is channel bonding. There is only space for one bonded channel in the 2.4 GHz band which, if utilized, would increase the probability of co-channel interference and make channel planning even more complex.
Conclusion
Last week, at the Gartner Mobile & Wireless Summit in Chicago, Michael King and Timothy Zimmerman gave a presentation on Next-Gen WLANs. In their presentation, they said that 802.11n networks are faster, cheaper, more secure, more reliable, and better managed than the wired infrastructure deployed in most enterprises today. Additionally, they said enterprises should align networking investments to an all-wireless office. I agree with them. But to maximize your chance of success, do it in 5 GHz.
Are you legally liable for running an open wireless network?
Earlier this week, I read an interesting blog post discussing the legal aspects of whether you should secure your home wireless network or leave it unencrypted. The post was actually written by a good friend of mine, Aamir Lakhani, who blogs at http://www.assassin711.com and micro-blogs on Twitter @Assassin711.
I wrote a blog post about it over at Computerworld, including my opinion on running open wireless networks.
http://blogs.computerworld.com/legal_aspects_of_running_an_open_wireless_network
Read it. Digg it. Comment on it.
Or comment on it here… What do YOU think? Should people secure their home wireless networks? Why or why not? Should people be concerned about their data ?
802.11n Deployment Considerations – Cabling
My 802.11n How Stuff Works Series was so popular, I thought I would start another series. This time I am going to talk about the various deployment considerations for 802.11n networks, such as:
- Cabling
- Power
- Trobleshooting/Analysis Tools
- WIDS/WIPS Sensors
- Etc.
Let’s take a look at the first of these considerations, cabling. With 802.11n, the data rates are drastically improved. Rates can be as high as 600 Mbps, but most practical implementations of 802.11n today have data rates of approximately 300 Mbps.
Therefore, the cable used should have higher capacity than 10/100 Mbps. What cables have 1 Gbps cabability? Category 5e or Category 6 cables can support the neccessary speed for 802.11n networks. IEEE 802.3ab also specifies 1000-Base-T over Category 5 cables, although I would personally recommend Cat 5e or Cat 6 cable.
Many newer access points or arrays have multiple physical interfaces to include console ports, 10/100 out of band management ports, and one or more 10/100 or Gigabit uplink ports. If your access points or arrays support multiple uplink ports, you should run separate cables to each.
Many times the multiple uplink ports can be configured in several different “modes” to include daisy chaining, port failover, port mirroring, or 802.3ad link aggregation. In port failover mode, running multiple uplink cables gives you a level of redundancy to survive a single port failure on either the access point or the uplink switch, increasing the overall reliability of the system.
- Related Posts:
An Information Security Place
If you are wondering why I didn’t post yesterday, it is because I served as a guest author on another blog, An Information Security Place. This blog was created by a friend and former colleague of mine, Michael Farnum. It is *really* popular – you should check it out! How popular do you ask? Well, if you type “an information security place” into the main page of Google, you will get approx. 25 million results. That is pretty impressive, considering the terms “802.11n” and “WiFi hotspots” only return approx. 12 million results combined.
My post yesterday was titled Factors Determing Installed WLAN Quality, and came out of a phone conversation that I had with Veriwave’s CTO and VP of Marketing earlier in the week. We spoke about the focus on wireless coverage and low interference when field testing WLANs. At a high level, we all agreed there were many other factors to consider, shown in the chart below:
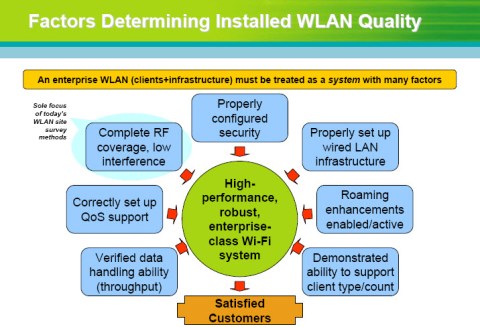
Factors Determining Installed WLAN Quality
Check out the post at An Information Security Place. Happy Reading!
Take Note of This!
Just a quick note… on the importance of taking good notes. 🙂
I am deploying 150+ Xirrus arrays for a elementary school district here in Phoenix, Arizona. If you have been following my blog, you have seen several posts about pre-implementation planning.
We have moved past the project planning stage and into project implementation. We have configured all the devices to meet the business and technical requirements of the district and have now begun physically mounting our WiFi arrays.
If you are unfamiliar with Xirrus, we aggregate multiple radios into a single platform along with a full layer 2 non-blocking switch, dedicated threat sensor, stateful firewall, and spectrum analyzer. This allows us to provide the same coverage and capacity as other vendors with 75% less devices, cable runs, and switch ports. We also don’t add any equipment to your IDF closets and consume considerably less power.
While we deploy considerably less devices, it is still imperative to note of all installation details. While mounting the devices, it is important to take note of the location, IP address, MAC address, and device serial number. You should also note any relevant details about the environment such as exisiting rogue/SOHO APs and potential sources of interference such as microwave ovens or large motors . Lastly, note any follow up items such as where new cable runs are needed or where legacy APs (which in this case, are Cisco) need to be removed. Be sure to assign each of the follow-up activities to a responsible party as well as assign a specific deadline for accountability.
Also take digital photos. They shouldn’t replace your notes, but as the saying goes, “A picture is worth a thousand words”. Happy note taking!
When to Perform Pre-Implementation Planning (3rd in a Series of 3)
Here is the previous portion of this particular post.
In the first two parts of this post, I spoke about the “what” and the “who” of implementation planning. Specifically I talked about pre-implementation checklists and pre-implementation conference calls. I also talked about getting buy in from senior management and taking a top down approach towards planning.
Now I tackle the question of when to preform preimplementation planning. While it is mostly common sense, my answer is “not too soon, and not too late”. I believe the sweet spot is usually 1-2 weeks before the beginning of the project. For longer projects with more detail, it may be neccessary to begin planning even sooner. For short projects (less than a week), pre-implementation planning may be done 2-3 days before the official start of the project. At that time, an official kickoff meeting may be required. We will explore the timing, audience, and agenda of kickoff meetings in a future post.
 Leave a comment
Leave a comment
![[LinkedIn]](https://i0.wp.com/farm4.static.flickr.com/3477/3463037125_247575d1f3_m.jpg)
![[LinkedIn]](https://i0.wp.com/farm4.static.flickr.com/3598/3463037145_924738ec38_m.jpg)
You must be logged in to post a comment.